Lenam Blog
RSS FeedHello, welcome to Lenam's personal blog. Here you will find information about CTFs, hacking, programming, artificial intelligence, and technology in general.
I hope you find this information helpful, just as the information others selflessly shared on the internet was helpful to me at the time.
Important Notice
The content presented on this website is intended solely for educational purposes, learning, and practice in pentesting and capture the flag (CTF) competitions. I am not responsible for the misuse of the information shared here.
Read the blog posts or check About for more info.
Featured
Browser Agent v86 POC: a Linux VM, an LLM, and agent tools inside the browser
 Published:
Published:With Browser Agent v86 POC, you can test a Linux x86 VM, chat with a local LLM, and automate tasks inside the VM, all from the browser. It is private and free: everything runs on your own machine, without relying on external servers.
WriteUp Latest Was A Lie - HackMyVM
 Published:
Published:Write-up for the Latest Was A Lie machine (HackMyVM): a Linux lab with web services and Docker, where a supply-chain angle—replacing or tampering with the image the stack deploys—leads into host foothold and privilege escalation.
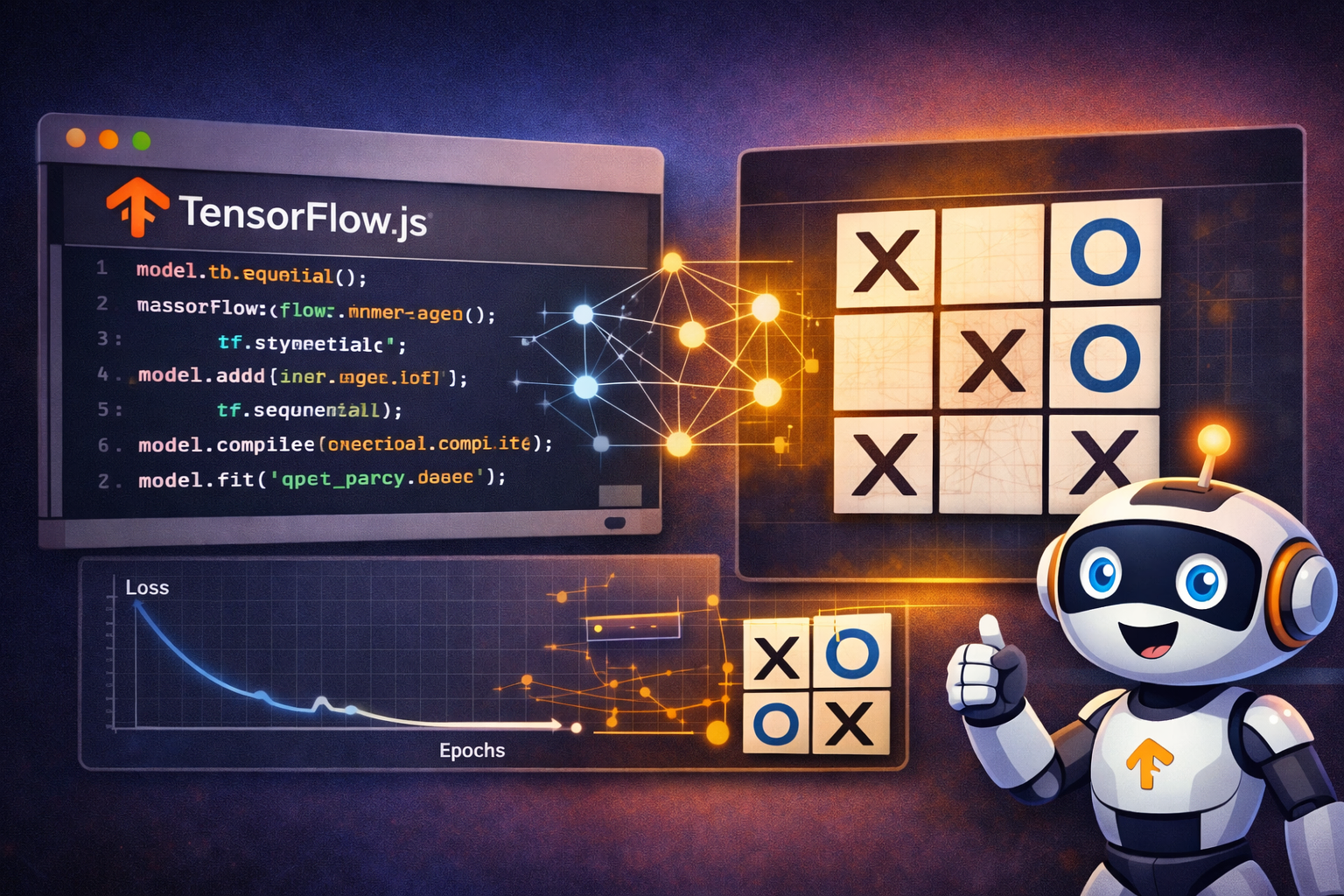
TensorFlow.js: AI and machine learning models in the browser
 Published:
Published:Create, train, evaluate and save a machine learning model directly in the browser with TensorFlow.js. Interactive tic-tac-toe demo with a local dataset, Web Workers and IndexedDB.
WriteUp Shadow Blocks - Vulnyx
 Published:
Published:Writeup of the Shadow Blocks machine (Vulnyx): iSCSI exploitation and disk data recovery to leak credentials, and unprotected NFS for privilege escalation.
Recent Posts
WriteUp GameShell5 - HackMyVM
Published:Writeup of the GameShell5 machine from HackMyVM: web enumeration, JavaScript deobfuscation, credential generation with LessPass, and privilege escalation through Copy Fail.
Transformers.js: language models and ML in the browser
Published:Run AI models directly in the browser with Transformers.js and Hugging Face. Interactive chat demo with an LLM using WebGPU (GPU) or WASM (CPU), no server, free and 100 % private.
WriteUp Ipeuveseis - TheHackersLabs
Published:Writeup for the "Ipeuveseis" challenge from The Hackers Labs, focused on attacking IPv6 services, container hopping and privilege escalation. Perfect for practicing pentesting techniques in containerized IPv6 environments.